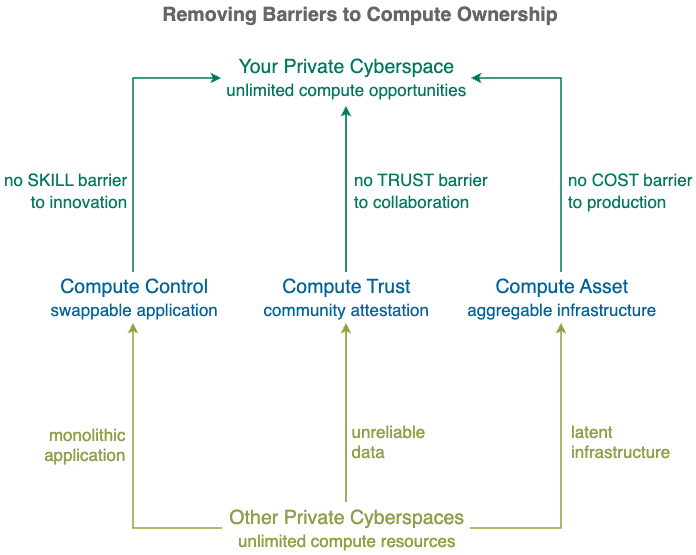
Private Cyberspace removes the skill, cost and security barriers to compute ownership, empowering everyone to regain CONTROL, ASSET, TRUST currently lost to Cloud Platforms.
Private Cyberspace boosts innovation, production and collaboration by removing cloud bottlenecks.
Evolve from a cloud compute user to a personal compute owner by creating your private cyberspace with just ONE CLICK
Be a compute owner instead of user, take the CONTROL of your digital life and VALUE of your data assets back from cloud platforms by creating your own private cyberspace .
1. Why Private Cyberspace ?
Transfer asset and control from Cloud Platforms to you.
Data is your most important asset – knowing or disclosing just ONE extra piece of data could change your life. Yet currently most of your data is stored remotely on Cloud Platforms, controlled and processed by parties that have DIFFERENT interests and aspirations to you.
You interact through their interfaces and you play by their rules, basically you have lost control – your most important asset is NO longer yours.
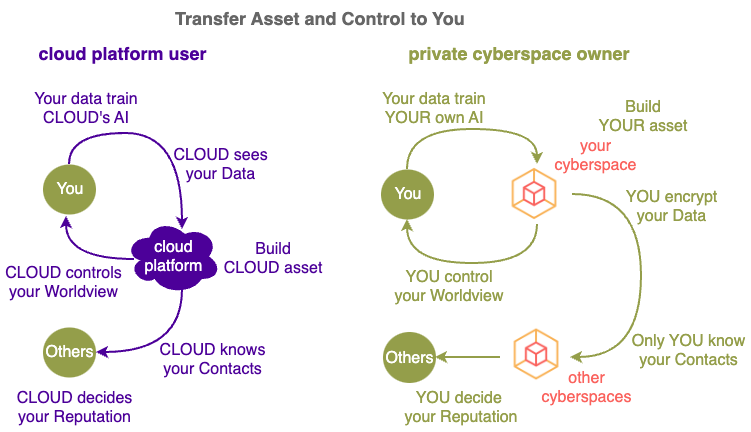
With Private Cyberspace you take back control of your digital life, data from every minute of your day is used to build up YOUR digital assets, instead of building up the Cloud's digital assets.
Beyond interacting within your immediate surroundings (the few metres that your eyes can see, hands can reach), the cyberspace has largely taken over most interactions you have in the physical space. The detrimental impact Cloud Platforms have on your digital world passes straight to your physical world.
However, unlike the physical space there is little diversity of ownership in the cyberspace, billions of individuals are interacting on dozens cloud platforms.
A cyberspace that is owned by just a just few service providers affect your life (from what you buy to what you think) in many negative ways. For example:
- the technical progress of the world's population is limited to the innovations made by just a few cloud platforms.
- individuals with different aspirations, cultures, interests etc. are confined to operate under the same set of rules (algorithms) on cloud platforms.
- cloud services are based on platform profits instead of user interests.
Without much competition in the cyberspace, ALL major cloud platforms (Apple, Google, Meta etc.) take money from 3rd parties in order to alter your behaviour (e.g. through advertisements, recommendations, influencers etc.) in ways that are advantageous to the 3rd party - not to you.
2. What is Private Cyberspace ?
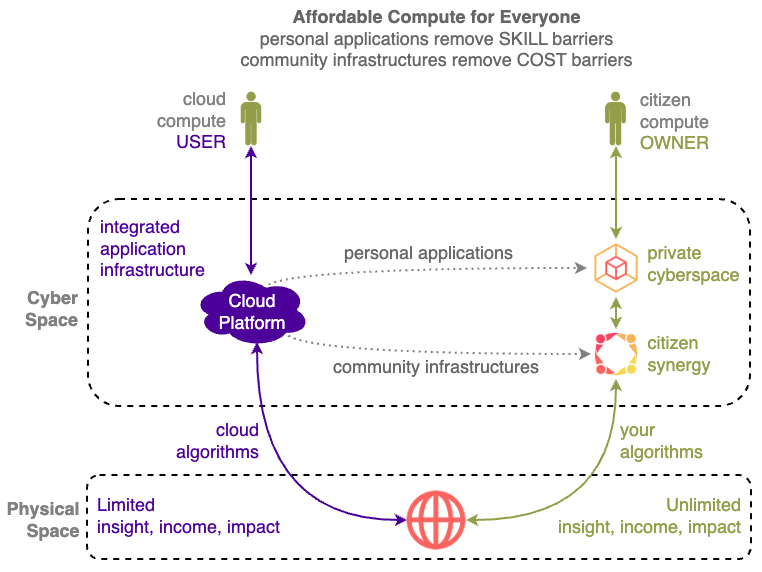
Private Cyberspace is a new compute paradigm that provides compute power to EVERYONE, from refugees to billionaires,
breaking the compute oligopoly
to break free from cloud control by processing their data by Importing Compute instead of Exporting Data to the cloud.
control your digital life by computing yourself and interacting directly
In order to provide abundant compute to everyone, no matter their wealth or knowledge levels, SKILL and COST barriers to Citizen Compute are removed by breaking up monolithic Cloud Platforms into billions of independent personal applications and community infrastructures.
-
No Skill Barrier
Non-technical owners can customise their Private Cyberspaces with millions of software application by simply mixing and matching them like toy bricks. -
No Cost Barrier
Owners can aggregated the latent infrastructures worldwide to
Will your Private Cyberspaces have enough compute ?
Experience Citizen Compute . . . with just ONE CLICK.
2. What is Private Cyberspace?
Compute Transfer asset and control from Cloud Platforms to you.
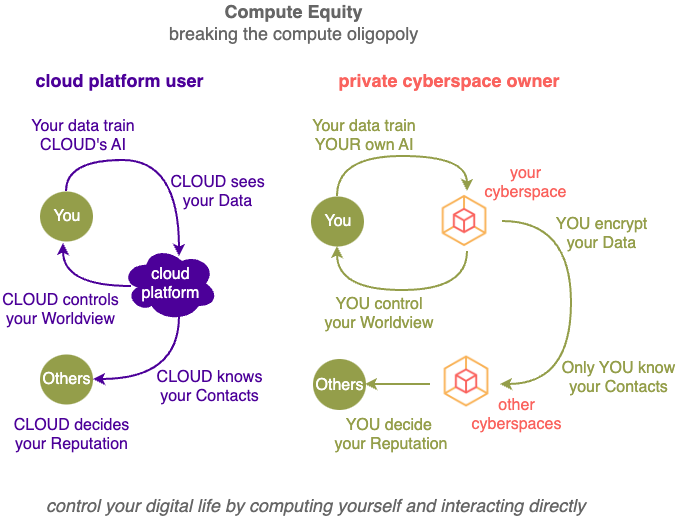
Private Cyberspace gives you an exclusive space to store and add value to your data, transforming you from an information user of cloud platform assets to an information owner with your own assets.
You are not longer a PASSIVE user building up CLOUD platform assets, you are now an ACTIVE owner building up YOUR own assets in your Private Cyberspace.
Similar to the benefits of owning traditional assets:
- owning your home (instead of staying in a rented room)
- driving your car (instead of waiting for buses or taxis)
the benefits of upgrading from a cloud platform user to a Cyberspace owner are substantial - Private Cyberspace can improve your digital life in more than 40 amazing ways.
As an analogy, many people cannot leave abusive relationships because they have no where to stay, Private Cyberspace gives your data a secure and productive place to stay, so you have the ability and confidence to leave the existing abusive relationship with the Cloud Platforms, with just ONE CLICK.
2. How ?
How does Private Cyberspace work?
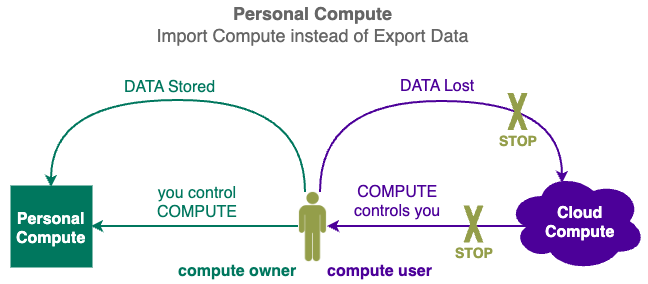
Import Compute instead of Export Data
Data is not useful by itself, it needs compute power to process it in order to create value.
Information Asset = Compute + Data
- Currently DATA is given to those with COMPUTE power (Cloud Platforms)
- Private Cyberspace gives COMPUTE power to those with DATA (you)
Private Cyberspace reverses the current data processing flow, instead of having to export your data to cloud platforms for processing, you import compute to process your data yourself ... with just ONE CLICK.
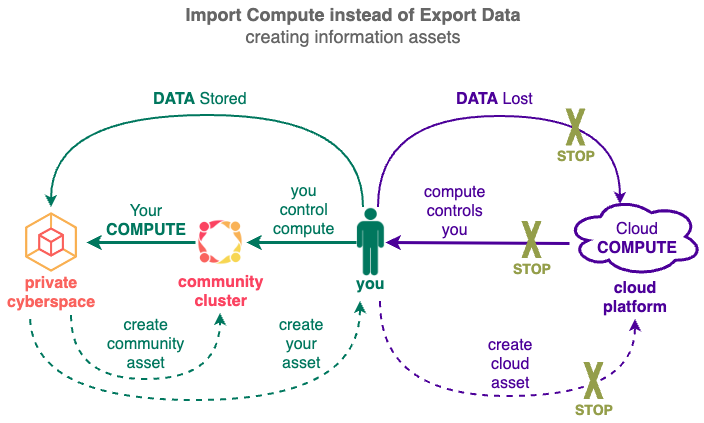
Instead of the Cloud both storing and processing your data to create information asset for itself, you now store data in your Private Cyberspace and , processed in ways you have control
3. Back to the Future
Similar to what the microprocessor did to the mainframes 50 years ago, Private Cyberspace enables the massive global decentralisation of computing.
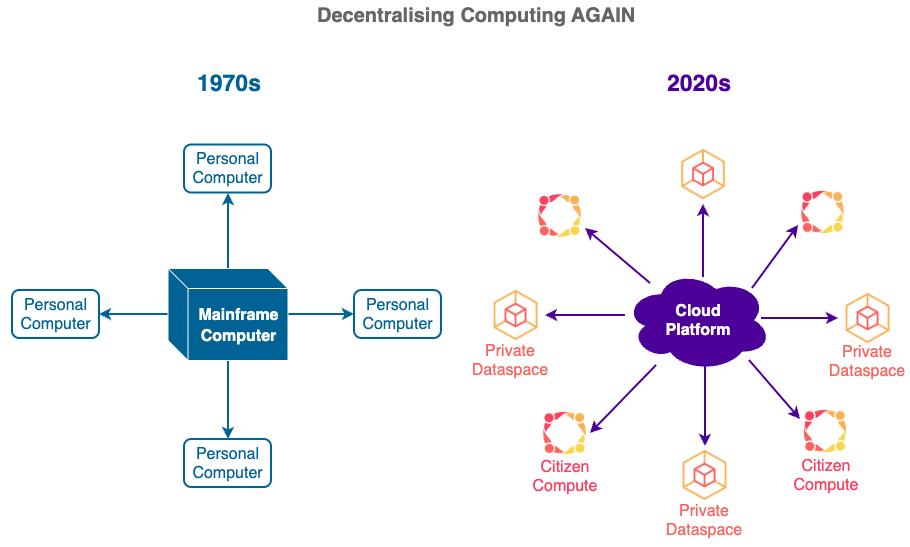
It is ironic that the companies that once drives the decentralisation computing efforts in the 1970s (e.g. Apple, Microsoft) are now dominant in driving the centralisation efforts.
Private Cyberspace reintroduces decentralised personal computing, so people can once again build up and control their own information spaces, just like their physical spaces e.g. their homes!